20 Easy Ways For Deciding On A Zk-Snarks Wallet Website
Wiki Article
"Zk Power Shield." How Zk-Snarks Can Hide Your Ip Address And Your Identity From The Internet
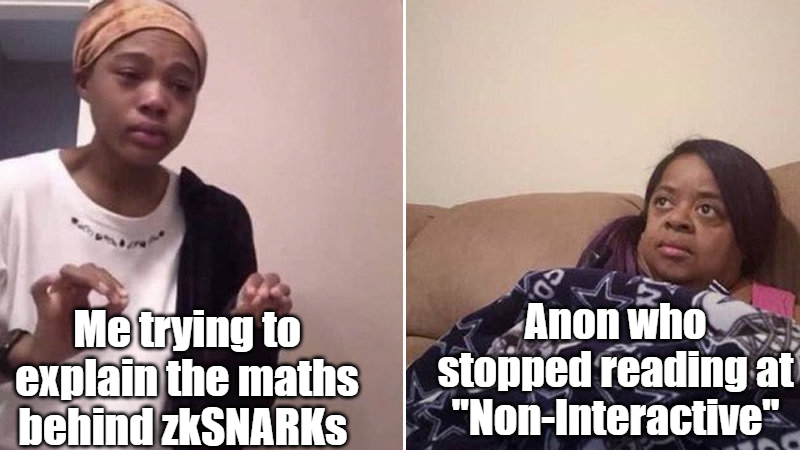
The privacy tools of the past employ a strategy of "hiding among the noise." VPNs route you through another server, and Tor will bounce you through networks. It is a good idea, however it is a form of obfuscation. They hide sources by shifting them away, and not by convincing you that it does not need to be made public. zk-SNARKs (Zero-Knowledge Short Non-Interactive Arguments of Knowledge) introduce a distinctive paradigm in which you could prove you're authorized to do something with no need to disclose who that. With Z-Text, you could broadcast an email directly to BitcoinZ blockchain. This Blockchain can determine that you're a genuine participant, with an authorized shielded email address however it's not able to identify which account sent it. Your identity, IP as well as your identity in this conversation is mathematically illegible to the outsider, yet in fact, it's valid and enforceable to the protocol.
1. The Dissolution Of the Sender-Recipient Link
Text messages that are traditional, even without encryption, can reveal the link. A observer sees "Alice is in conversation with Bob." ZK-SNARKs destroy this connection completely. If Z-Text emits a shielded signal and the zk-proof is a confirmation that an operation is genuine, that is to say the sender's balance is sufficient and that the keys are valid--without divulging addresses of the sender and the recipient's address. In the eyes of an outsider, it is seen as a encryption noise coming from the network itself, however, it's not coming from any particular person. The connection between two particular human beings becomes impossible for computers to determine.
2. IP Protection of IP Addresses is at the Protocol Level, not the App Level
VPNs as well as Tor secure your IP in the process of routing traffic via intermediaries. But those intermediaries also become new points of trust. Z-Text's usage of zkSNARKs indicates that your IP's address will never be relevant in the verification process. In broadcasting your protected message to the BitcoinZ peer-to'-peer community, you represent one of the thousands of nodes. The zk-proof assures that even anyone who observes the networks traffic, they are not able be able to connect the received message with the wallet which started it all, because the document doesn't have that info. The IP's information is irrelevant.
3. The Abolition of the "Viewing Key" Difficulty
In many blockchain privacy systems the user has a "viewing key" that lets you decrypt transaction information. Zk-SNARKs, which are part of Zcash's Sapling protocol and Z-Text allows selective disclosure. You are able to demonstrate it was you who sent the message without revealing your IP, your transactions in the past, or the complete content of the message. The evidence itself is all that is you can share. Granular control is not feasible when using IP-based networks where sharing the content of the message automatically exposes the IP address of the originator.
4. Mathematical Anonymity Sets That Scale Globally
When you are using a mixing or VPN in a mixing service or a VPN, your anonymity is just limited to users in that specific pool at this particular time. With zkSARKs you can have your privacy will be guaranteed by every shielded address across the BitcoinZ blockchain. Because the evidence proves there is some secured address, one of which is potentially millions of others, and does not give any suggestion of which one. Your protection is shared across the entire network. The privacy you enjoy isn't in smaller groups of co-workers that are scattered across the globe, but in an international gathering of cryptographic IDs.
5. Resistance to Timing Analysis and Timing Attacks
Effective adversaries don't simply look up IP addresses. They analyze how traffic flows. They look at who sends information at what times, and compare events. Z-Text's use of zk-SNARKs, coupled with a mempool of blockchain allows the decoupling operations from broadcast. You may create a valid proof offline before broadcasting it when a server is ready to send it. Its timestamp for presence in a block not directly linked to the instant you made it. restricting timing analysis, which often degrades anonymity software.
6. Quantum Resistance by Using Hidden Keys
IP addresses do not have quantum resistance. In the event that an adversary could detect your IP address now and then break your encryption later and link the data to you. Zk - SNARKs, like those used in Z-Text, protect your key itself. Your public key is never publicly available on the blockchain due to your proof of identity confirms you've got the right key however it does not reveal the exact key. A quantum computer, even in the future, would view only the proof it would not see the key. The information you have shared with us in the past is private because the secret key used make them sign was never made available and cracked.
7. Unlinkable Identities in Multiple Conversations
With just a single wallet seed You can also generate multiple protected addresses. Zk-SNARKs enable you to demonstrate that you own one of the addresses without sharing which one. This means you can have several conversations in ten various people. No user, nor even the blockchain itself could track those conversations through the same underlying wallet seed. The social graph of your network is mathematically fragmented by design.
8. suppression of Metadata as a target surface
Spies and regulators often claim "we aren't requiring the content but only metadata." Ip addresses serve as metadata. Your conversations with whom you are metadata. Zk-SNARKs are unique among security technologies due to their ability to hide metadata at the cryptographic level. They do not include "from" or "to" fields that are plaintext. There's no metadata attached to make a subpoena. There is just the proof, and the proof provides only proof that an decision was made, and not whom.
9. Trustless Broadcasting Through the P2P Network
When using a VPN then you can trust the VPN provider to never log. When you utilize Tor You trust your exit node to never record your activities. By using Z-Text, you transmit your zk-proofed transaction BitcoinZ peer to-peer platform. Connect to a handful of random nodes, send the data, then switch off. Nodes are not learning anything, as there's no evidence. They cannot even be certain that you're actually the creator, considering you could be sharing information for someone else. Networks become a trusted source of information that is private.
10. "The Philosophical Leap: Privacy Without Obfuscation
Zk-SNARKs also represent one of the most philosophical transitions over "hiding" into "proving by not divulging." Obfuscation technologies accept that the truth (your IP, your personal information) is dangerous and must be kept hidden. Zk-SNARKs acknowledge that the truth cannot be trusted. The system only has to understand that you're registered. Moving from a reactive concealing towards proactive non-relevance is at fundamental to ZK's protection. Identity and your IP is not hidden; they have no relevance to the operation of the network therefore they're never required and never transmitted or made public. Have a look at the most popular shielded for more advice including text messenger, encrypted text message app, text privately, encrypted app, encrypted app, encrypted text app, messages messaging, private text message, message of the text, encrypted messenger and more.
"The Mutual Handshake: Rebuilding Digital Trust in the Zero-Trust World
The internet is built on an infrastructure of connection implicit. Anyone can reach out to anybody. Anyone is able to follow anybody on social media. This transparency, although valuable was a source of trust. The occurrence of phishing attacks, spam as well as harassment are all symptoms of a system where connections are not subject to any or consent. Z-Text reverses this belief through the handshake that is cryptographic in nature. Before any byte of information flows between two people they must both agree for the connection to take place, and this consent is ratified by the blockchain and confirmed by zk-SNARKs. This simple act--requiring mutual consent at the protocol level--rebuilds digital trust from the foundation up. This is akin to the physical world where you're not able to communicate with me until I have acknowledged you. I also cannot speak to you until I acknowledge me. In this age of zero credibility, the handshake becomes the basis of communications.
1. The handshake as the basis for a cryptographic ritual
In Z-Text, the handshake isn't just a standard "add contact" button. It's a cryptographic event. Partie A creates a connection request containing their public signature and a temporary permanent address. Party B will receive this request (likely in-band or via a open post) and produces an acceptance, which includes their public key. Parties B and A then come up with from a shared secret to establish the communication channel. This is a way to ensure that each participant has been actively engaged so that nobody can infiltrate the system without detection.
2. It's the Death of the Public Directory
Spam occurs because email addresses and telephone numbers are part of public directories. Z-Text is not a directory that's public. Z-Text's address is not published on the blockchain. Instead, it lies hidden inside protected transactions. Anyone who wants to contact you should have information about you--your personal identification, your QR code, or a shared security code to open the handshake. There's no search feature. This removes the principal source for unintentional contact. You are not able to spam an email address is not available.
3. Consent is a Protocol In no way is it Policy
With centralized applications, consent will be an important feature. One can deactivate someone's account after that person has contacted you, but they've already infiltrated your mailbox. The Z-Text protocol has consent integrated into the protocol. It is impossible to send a message without a prior handshake. A handshake is null proof that the parties have agreed to the link. The protocol is a way to enforce consent, rather than just allowing users to react in breaking. Architecture itself is respectful.
4. The Handshake as a Shielded An Event
Since Z-Text is based on zkSARKs, the handshake itself can be private. When you accept a connection request, the handshake is protected. The person looking at it cannot discern that you and a different party have made a connection. Your social graph expands invisibly. The handshake occurs in digital dimness, visible only by only the two party. This is not the case with LinkedIn or Facebook the latter, where each interaction is broadcast.
5. Reputation and Identity Without Identity
Which one do you decide to hold hands with? Z-Text's model allows for the creation of reputation systems that don't rely on revealing identity. Because connections are private, it's possible that you'll receive a "handshake solicitation from someone you share the same contacts. This common contact may be able to vouch that they are trustworthy by a cryptographic attestation, with no disclosure of who any of you. In this way, trust becomes a transitory and non-deterministic the person you trust because someone you trust believes in them, without ever learning about their identity.
6. The Handshake as Spam Pre-Filter
Even with the handshake requirement even a zealous spammer can make thousands of handshake requests. Each handshake, much like any message, has the payment of a small fee. It is the same for spammers. exact same cost at connection stage. For a million handshakes, it costs about $30,000. Although they may pay an amount, they'll still want you for them to pay. In addition to the fee for handshakes, micro-fees can create two obstacles to economic growth that causes mass outreach to be financially unsustainable.
7. The Recovery and Portability of Relationships
If you restore your ZText account from the seed phrase all your contacts recover also. But how does the application identify your contacts without a centralised server? The protocol for handshakes writes a minimal, encrypted record to the blockchain. It's a reminder that connections exist between two secure addresses. Once you restore, your wallet checks for handshake notes before rebuilding your contacts list. The graphs of your social networks are stored on the blockchain, but only visible to you. Your network is as flexible just as your finances.
8. The Handshake as a Quantum-Safe Engagement
A handshake that is mutually agreed upon creates a sharing of a secret between two persons. This secret can be used as keys for upcoming communications. As the handshake itself protected by a shield that never will reveal the keys of public parties, it can be a barrier to quantum encryption. The adversary is unable to break it to reveal what the relationship was because the handshake didn't reveal any key public. The promise is eternal, nevertheless, the handshake is invisibly.
9. The Revocation as well as the Un-handshake
There is a risk of breaking trust. Z-Text allows an "un-handshake"--a cryptographic cancellation of the connection. When you block someone, your wallet emits a "revocation" confirmation. This proof informs the system that any future messages sent by the party are to be rejected. As it's a chain transaction, the rejection is permanent and can't be disregarded by clients of either party. The handshake could be modified by a person who is not as definitive and legally binding as the initial agreement.
10. The Social Graph as Private Property
Finally, the mutual handshake alters the ownership of your social graph. When you are on a central network, Facebook or WhatsApp possess the entire graph of the people who talk to whom. They mine, analyze them, and eventually sell it. Your Z-Text social graph is encrypted and saved on the blockchain. It is accessible only by only you. Nobody else owns the maps of your relationships. Handshakes ensure that the unique record of your contact remains with you and the contact you have made, and is cryptographically secured away from others. Your network is your property rather than a corporate resource.
